Data Breach Dilemma
In 2023, the IBM Cost of a Data Breach Report revealed alarming statistics. The global average cost of a data breach has surged to $4.45 million, a notable 15% increase from 2020. In response to this growing threat, 51% of organizations are planning to bolster their cybersecurity spending. Shockingly, the healthcare sector bears the brunt of these breaches, with an average cost of $10.93 million, indicating a staggering 53.3% increase over the past three years.
The Tausight GEN3 Model: A Data Security Game-Changer
Data loss prevention (DLP) tools have been the stalwart defenders of sensitive organizational data. However, they find themselves in an era of dynamic threats with significant limitations. In this article, we introduce “Tausight GEN3 AI solution” as a revolutionary approach to data security. We will explore the deficiencies of traditional DLP tools and present a more effective alternative.
The Shortcomings of Traditional DLP Tools
Traditional DLP tools, despite their value, grapple with several critical challenges:
- Rule-Based Limitations: Traditional DLP relies on predefined rules, rendering them inflexible and incapable of adapting to evolving threats. These rules struggle to keep pace with emerging data types and threats. Let’s consider a healthcare organization that uses a traditional DLP system to protect patient records and ensure compliance with healthcare data privacy regulations. The DLP tool is configured with a set of predefined rules that flag any document containing patient names, medical record numbers, and specific medical conditions. Now, imagine a scenario where a new type of data threat emerges in the form of a previously unknown medical condition that becomes a subject of concern. In this case, the DLP system’s rules do not include this new medical condition in its predefined criteria because it was not known when the rules were initially set up. A medical researcher within the organization creates a text file discussing this new medical condition and its potential implications. This text file contains important, sensitive information that the DLP system should ideally detect and protect. However, since the DLP tool relies on predefined rules, it fails to recognize the newly emerging medical condition within the text file. The tool lacks the flexibility to adapt to this evolving threat because it has not been updated to account for this specific type of sensitive data. As a result, the text file goes undetected, and the organization remains unaware of the potential data breach risk associated with this new medical condition.
- False Positives: DLP tools are infamous for generating false alerts, resulting in user complacency and diminishing their overall effectiveness. A hospital employs a traditional DLP tool to safeguard patient records and sensitive medical information. The system, configured with strict rules, often triggers false alerts, mistakenly flagging benign medical terms or standard procedures as potential data breaches. For instance, routine medical terms like “HIPAA” or “patient referral” get misinterpreted as sensitive data, generating frequent false alarms. These continuous false positives cause alarm fatigue among the hospital staff. Over time, the security team and healthcare professionals start disregarding these alerts assuming they are likely false positives, leading to complacency. As a result, the DLP tool’s effectiveness diminishes, potentially allowing genuine security threats to slip through unnoticed.
- Lack of Context Awareness: Traditional DLP tools often falter in distinguishing between accidental data exposure and malicious intent due to their limited contextual understanding. Consider a scenario where a medical researcher is collaborating on a groundbreaking study and needs to share medical records with colleagues. The traditional DLP system, configured with rigid rules, fails to discern the context behind this data sharing. Despite the legitimate need for collaboration, the system, lacking contextual understanding, flags this data transfer as a potential breach. The DLP tool cannot differentiate between the researcher’s authorized sharing for critical research purposes and a malicious attempt to expose sensitive patient information. The absence of context awareness leads to an inability to distinguish between benign, authorized data sharing and intentional, unauthorized data exposure, creating challenges in accurately identifying genuine threats.
- Inefficient Scalability: Scaling traditional DLP can be a complex, resource-intensive task, demanding significant human and time resources for rule updates, incident response, and maintenance. As the hospital’s data volume increases due to the digitalization of patient records and the integration of new medical technologies, the traditional DLP system struggles to handle the growing scale of information. To adapt, the security team needs frequent rule updates and adjustments to accommodate the expanding data types and sources. This process demands a substantial allocation of human resources and time. Technicians need to constantly tweak and update rules, slowing down incident response times. Maintenance becomes a continuous, labor-intensive task, as the system’s inability to efficiently scale with the increasing data volume leads to a strain on the resources required for rule management and system upkeep.
- Challenges with False Negatives: Traditional DLP tools are plagued by false negatives, failing to detect and alert genuine security breaches, thereby exposing organizations to significant risks. Consider a situation where a malicious actor gains unauthorized access to the hospital’s patient database. The traditional DLP system, due to its reliance on predefined rules, fails to recognize this unusual activity as a potential security breach. The attacker, using sophisticated methods to access and exfiltrate patient data, goes undetected by the DLP tool, leading to a false negative. The system’s inability to adapt to evolving threats and tactics results in a failure to alert the security team of this genuine security breach. As a consequence, sensitive patient data is compromised, potentially leading to severe repercussions such as breaches of patient privacy, legal implications, and damage to the hospital’s reputation. The limitations of the traditional DLP tool in detecting such sophisticated breaches highlight the significant risks posed by false negatives, leaving the organization vulnerable to security threats.
The False Comfort of Traditional DLP and Its Potential Risks
Relying heavily on traditional Data Loss Prevention (DLP) systems may create a false sense of security, thereby subjecting organizations to multiple risks. These risks encompass overconfidence in the system, an inability to adapt to evolving threats, limited visibility into data usage, and potential compliance and legal perils. According to Gartner, it’s worth noting that over 35% of DLP implementations have encountered significant challenges. The conventional approach to DLP, although offering a semblance of security, presents inherent vulnerabilities and limitations, where attempts to address false positives inadvertently lead to a significant rise in false negatives. This shift not only influences perceptions but also intensifies the organization’s exposure to undetected security breaches, potentially leading to severe repercussions.
The Costs of Traditional DLP
Implementing and maintaining traditional DLP solutions involves an array of costs, such as:
- Initial Investment: Organizations must invest in acquiring DLP software, hardware, and licenses, resulting in substantial upfront expenses.
- Human Resources: Managing and upkeeping traditional DLP tools demands a dedicated team of IT professionals responsible for configuring and updating rules, handling incidents, and conducting regular maintenance.
- Time and Productivity Loss: False positives and manual rule management can lead to a decrease in employee productivity as users are persistently interrupted by unnecessary alerts.
- Training and Skill Development: Organizations must allocate resources to train their IT staff in effectively managing and operating DLP tools, necessitating ongoing training to keep up with evolving threats and tool updates.
- Compliance and Legal Costs: Failing to meet compliance requirements can result in legal fees, fines, and potential business loss due to reputational damage.
- Scalability Challenges: As organizations expand, they may need to invest in additional DLP resources and expertise to maintain an effective level of security, which can be resource-intensive.
Introducing the Tausight Gen3 Model for Data Security
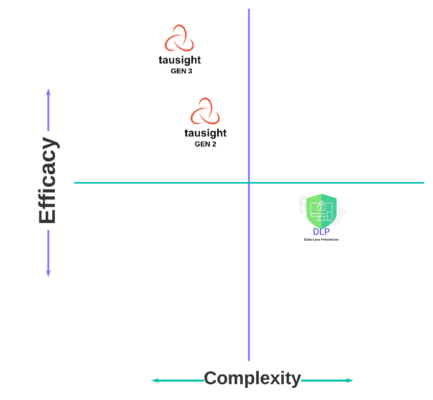
Complexity vs. Efficacy
To combat the limitations of traditional DLP, Tausight brings forth a transformative approach:
- AI and Machine Learning Integration: “Tausight Gen3” model leverages advanced AI and machine learning models to gain a deeper understanding of data context. This empowers dynamic, self-improving systems capable of recognizing evolving data patterns.
- Behavior-Based Approach: In contrast to rigid rules, “Tausight Gen3” focuses on behavioral analysis, learning how data is utilized within an organization and detecting anomalies that hint at potential security breaches.
- Reduced False Positives: By employing AI for context-aware analysis, “Tausight Gen3” significantly curtails false positives, making alerts more meaningful and actionable.
- Adaptive Learning: “Tausight Gen3” remains in a constant state of evolution, continually learning from new data and emerging threats, thereby establishing a more robust and future-proof solution for data security.
- Scalability and Ease of Management: “Tausight Gen3” efficiently scales to cater to the needs of large enterprises, simplifying the complexity of manual rule management and maintenance.
- Cost Savings: Tausight’s AI-driven approach operates autonomously. It eliminates the need for dedicated teams to handle rule configurations, incident responses, and routine maintenance, allowing IT professionals to focus on more strategic tasks. This translates into not only considerable time savings but also a reduction in associated costs, making data security a more efficient and cost-effective endeavor.
In conclusion, traditional DLP tools, while valuable, have limitations that organizations must recognize. To address these limitations, organizations should consider advanced, AI-driven approaches like the Tausight GEN3 Model to enhance data security, overcome the shortcomings of traditional DLP, and mitigate the associated risks and costs.

